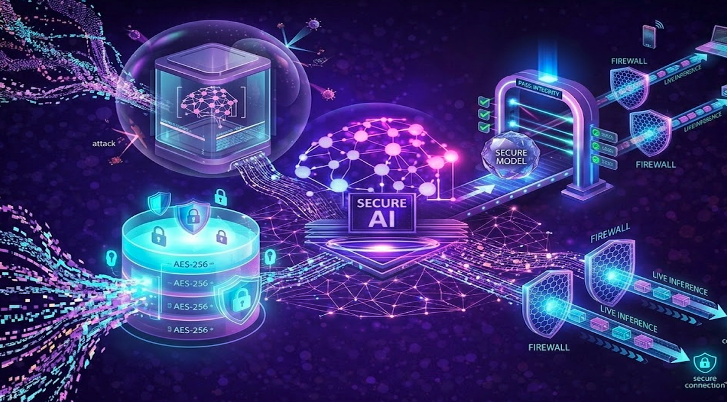
End-to-end AI security requires visibility, evaluation, and governance across the full lifecycle — not just point-in-time controls.
AI and machine learning systems have evolved far beyond static artifacts; today, they form dynamic, living pipelines. From the moment raw data enters the system, through experimentation, model training, and deployment, to ongoing inference and continuous refinement, these pipelines are in constant motion. At every step, unique risks emerge, yet remarkably, most organizations manage to secure only isolated segments of this critical lifecycle.
Traditional security measures, such as infrastructure hardening and access controls, are no longer sufficient. AI brings new challenges, from data integrity to unpredictable model behavior and dynamic third-party risks.
As enterprises accelerate AI adoption, pipelines are expanding faster than governance models can adapt. Data scientists iterate quickly. Foundation models are integrated from external repositories. APIs connect to external services in real time. The result is an operational reality where AI pipelines influence customer outcomes, financial decisions, and regulated processes without comprehensive oversight.
Securing the AI/ML pipeline end-to-end is no longer a technical optimization. It is a governance requirement.
How AI Expands the Traditional Security Perimeter
An AI/ML pipeline spans more than training code and deployment scripts. It includes data ingestion, preprocessing, feature engineering, model selection, experimentation environments, CI/CD workflows, containerization, inference endpoints, monitoring systems, and retraining loops.
Each stage introduces dependencies, expands trust boundaries, and adds security considerations.
Traditional software security models focus on static artifacts and predictable behaviors. But AI pipelines break the mold. They continuously evolve, adapting as data shifts, models are fine-tuned, and external services change in real time. This means risk is not just a deployment concern; it is woven throughout the entire pipeline lifecycle.
This difference is not merely procedural. It is structural, fundamentally shaping how security and governance must operate in AI systems.
| Dimension | Traditional Approach | AI-Era Reality |
|---|---|---|
| Primary Asset | Application code | Data, models, weights, and APIs |
| System Behavior | Deterministic and testable | Probabilistic and input-driven |
| Update Cycle | Controlled releases | Continuous retraining and tuning |
| Validation Focus | Code integrity and vulnerabilities | Data lineage, model behavior, and drift |
| Runtime Risk | Infrastructure compromise | Behavioral manipulation and output drift |
Security controls built for code do not automatically extend to training data or model weights. Validation processes designed for software releases do not account for adversarial prompting or silent model drift.
The surface area is broader, and the risks propagate differently.
The Silent Drift Problem in AI Systems
When an AI/ML pipeline is compromised, you usually do not see a dramatic system outage. Instead, you notice subtle shifts in behavior, changes that can quietly reshape outcomes and user experiences.
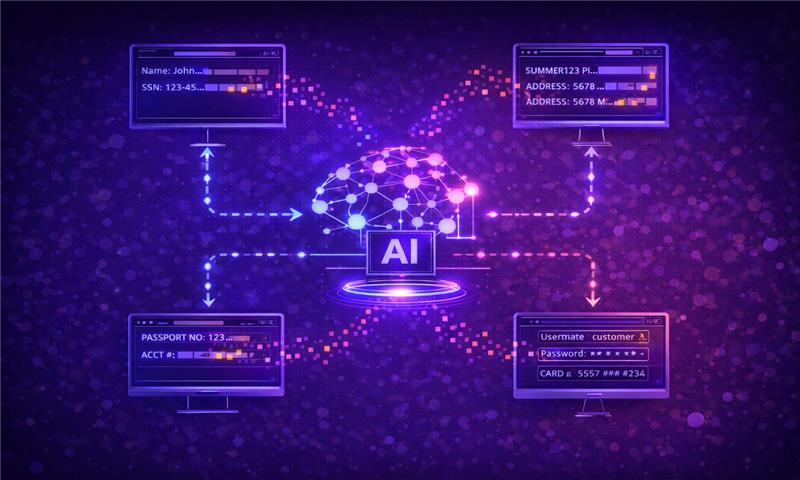
Data poisoning at the earliest stage can inject hidden biases or backdoors, waiting to be triggered by just the right input. During model development, using unvetted pretrained components can quietly embed unsafe logic or hidden dependencies. Even after deployment, third-party APIs might change their behavior unexpectedly, without warning or formal announcements.
Production introduces persistent challenges, including drift, shifts in data distribution, evolving user behavior, and models adapting via retraining or fine-tuning. If you do not continuously evaluate, systems can quietly move outside approved boundaries while still looking perfectly stable on the surface.
Detecting these issues is not easy. Traditional monitoring focuses on uptime and performance but rarely checks for intent, policy alignment, or vulnerability to adversarial attacks. A model might look accurate on paper while quietly drifting out of compliance or safety.
Risk spreads quietly across downstream applications, automated decisions, and customer-facing systems.
The Limits of Conventional Cybersecurity in AI Systems
Traditional security and compliance frameworks simply were not built for AI’s unique world, one where systems continuously learn from data and interact in real time with users.
Secure build pipelines can verify artifact integrity, but they do not check whether your training data is trustworthy. Vulnerability scans detect known software flaws but overlook threats such as prompt injection or model extraction. Access controls might determine who can deploy code, yet they cannot guarantee that your models behave safely and within acceptable risk boundaries.
This leaves organizations facing critical blind spots, especially when it comes to questions like:
- Do we know the lineage of the data used to train this model?
- Has the model been evaluated against adversarial or misuse scenarios?
- Can we detect behavioral drift before it impacts customers?
- Are third-party AI services governed under the same standards as internal systems?
Without clear answers to these questions, organizations are left navigating uncertainty, never fully confident in the security or compliance of their AI systems.
When AI Pipeline Risk Becomes Enterprise Risk
For boards and executive leaders, AI pipeline security is not just theoretical. It directly shapes regulatory compliance, customer trust, and financial results.
With regulators demanding full traceability and proactive risk management throughout the AI lifecycle, accountability for biased or unsafe outputs goes far beyond the data science team. It reaches across the entire enterprise.
Customer trust is just as fragile. One incident, whether it is manipulated outputs, exposed training data, or an unsafe recommendation, can quickly erode hard-won credibility. In regulated industries, these missteps can trigger mandatory reports or legal scrutiny.
Operational continuity is also on the line. As AI systems become central to critical workflows, from fraud detection to supply chain optimization, a single compromised or drifting model can disrupt business decisions at scale.
That is why accountability boundaries must be defined before an incident ever occurs.
Building a Secure and Governed AI Lifecycle
Securing your AI/ML pipeline starts with true visibility. You need a clear, real-time understanding of every dataset, model, framework, and service in play. Documenting lineage, from data ingestion to deployment, lays the foundation for trust and accountability.
Behavioral evaluation is just as critical. Do not just test for accuracy. Probe for adversarial resilience, misuse potential, and policy alignment. Evaluation is not a checkbox before launch; it is an ongoing commitment.
Continuous oversight in production is non-negotiable. Effective monitoring looks past performance metrics to catch behavioral drift, unexpected outputs, and changes in system dependencies.
Make documentation and traceability a living part of your operations, not a scramble during audits. Governance should always reflect the real-time state of the system, test results, and approval workflows.
Real pipeline security is not about a single control. It is an integrated discipline that brings together data governance, model risk management, and proactive runtime monitoring.
How Cranium Enables Continuous AI Oversight
Cranium empowers enterprises to put practical, end-to-end AI governance into action without slowing down innovation.
By giving organizations deep visibility into every model, dataset, and dependency across all environments, Cranium makes it possible to truly know your AI. Cranium Arena lets teams safely stress-test models against real-world adversarial and misuse scenarios before anything goes live, protecting your business from unwanted surprises.
In production, the Cranium platform keeps a watchful eye on behavioral risk, not just infrastructure metrics, so issues surface early instead of after impact. Cranium AI Cards turn documentation into a living, structured record of lineage, testing, and governance, making regulatory traceability straightforward and audit-ready.
The goal is not to hold innovation back. It is to make sure every step forward happens within clear, responsible risk boundaries.
The Future of AI Security Is Lifecycle Governance
The AI/ML pipeline is no longer a narrow development workflow. It is a distributed system spanning data, models, infrastructure, and runtime interactions.
Traditional security practices address part of the challenge. They do not account for behavioral risk, dynamic dependencies, or lifecycle drift. That gap creates exposure at scale.
As AI becomes embedded in enterprise decision-making, end-to-end pipeline governance becomes a strategic requirement. Visibility, evaluation, and continuous oversight must extend from data ingestion to production monitoring.
Securing AI is not about protecting a model in isolation. It is about governing the system that produces and sustains it.
Explore how Cranium helps enterprises govern and secure AI systems — schedule a personalized demo: cranium.ai/get-a-demo/