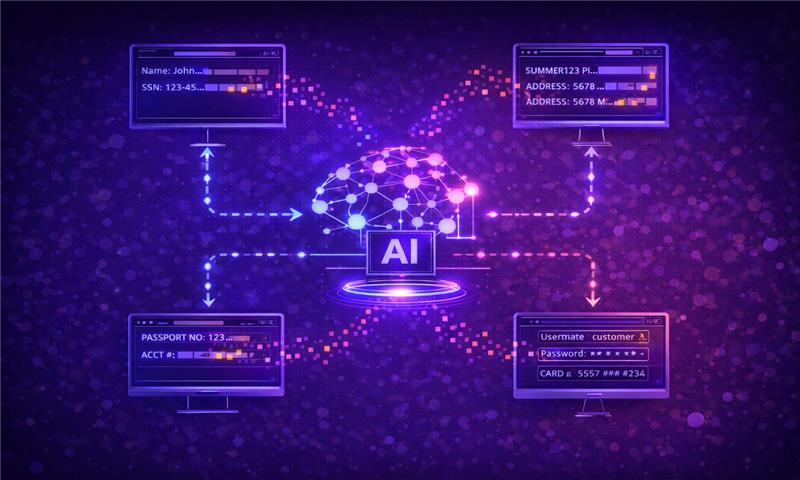
Because AI systems don’t need to be compromised to expose data. In many cases, they simply need to function as designed.
Most security leaders think of data leakage as something that happens after a breach. An attacker gets in. Files move. Alerts fire. But that’s not how AI systems fail.
Large language models and machine learning systems are built to absorb patterns from massive datasets. They generalize, infer, and reconstruct. That capability is what makes them powerful. It’s also what makes them risky.
If your AI models were trained on sensitive data, interact with proprietary systems, or retain conversational context, they may expose information in ways traditional security tools were never built to detect.
And the most dangerous leaks rarely trigger an alarm.
Key Takeaways
- AI models can expose sensitive training data, proprietary logic, and user information through normal interactions.
- Data leakage often occurs without exploitation — models may unintentionally reproduce memorized content.
- Prompt manipulation, model extraction, and API misuse can amplify leakage risk.
- Traditional DLP and network security tools are not designed to monitor model behavior.
- Effective defense requires lifecycle visibility: discovery, testing, monitoring, and governance.
- AI governance must extend beyond infrastructure to include model behavior and data lineage.
How AI Models Actually Leak Data
Data leakage from AI systems doesn’t always look like a breach. It often looks like a helpful response.
1. Training Data Memorization
Research has shown that large language models can memorize and reproduce parts of their training data, especially when it includes rare or unique sequences. In some cases, researchers have extracted private information from models by carefully crafting prompts.
If proprietary documents, customer records, or internal communications were included during fine-tuning, portions of that content may resurface under the right conditions.
The model isn’t “malicious.” It’s performing statistical reconstruction.
2. Prompt-Based Extraction
Even when models aren’t directly trained on sensitive data, they can expose information through contextual interactions.
Carefully structured prompts can coax models into revealing hidden system instructions, internal configuration details, or sensitive information from integrated data sources. When AI systems are connected to retrieval databases or enterprise APIs, the risk expands further.
From a logging perspective, these look like valid queries. From a governance perspective, they may represent unintended disclosure.
3. Context Retention and Session Leakage
Many enterprise AI systems retain conversation history to improve usability. That context persistence can become a leakage vector.
If session boundaries aren’t clearly defined, or if context isn’t properly isolated between users, information from one interaction may influence another. Even subtle context bleed can expose customer information or internal data.
In high-volume enterprise environments, this risk compounds quickly.
4. Model Extraction and Reverse Engineering
Attackers can use high-volume queries to approximate a model’s internal behavior, sometimes extracting proprietary decision logic or data correlations in the process.
This doesn’t always leak raw data. But it can expose patterns that reflect sensitive relationships embedded in training data.
The more valuable the model, the greater the incentive to extract it.
Why Traditional Security Tools Miss AI Data Leakage
Most cybersecurity programs focus on perimeter defense and explicit data movement. Firewalls monitor traffic flows. Data loss prevention tools inspect outgoing files. Identity controls manage access permissions.
AI data leakage doesn’t necessarily involve file transfers or unauthorized access. It can occur through legitimate API calls, valid prompts, or standard user interactions. From an infrastructure standpoint, nothing abnormal is happening.
What’s missing is behavioral visibility — the ability to detect when a model output crosses policy boundaries. Traditional tools can tell you where data moved. They can’t always tell you why the model produced it in the first place.
The Hidden Risk: AI as a Data Multiplier
AI systems don’t just store data. They amplify it.
A single fine-tuning dataset can influence thousands of outputs. A single integration with a CRM or knowledge base can expand exposure across departments. A single misconfigured retrieval pipeline can expose sensitive documents at scale. The risk is multiplicative.
| Dimension | Traditional Application Data Flow | AI-Driven Data Flow |
|---|---|---|
| Flow Structure | Linear and rule-based (input → logic → output) | Dynamic and context-driven (input → model inference → variable output) |
| Data Usage | Data processed per transaction | Data influences model behavior over time |
| Output Predictability | Deterministic and repeatable | Probabilistic and non-deterministic |
| Control Points | Clear validation and enforcement checkpoints | Fewer hard boundaries; behavior shaped by prompts and training |
| Risk Propagation | Errors are typically isolated to one function | Failures can cascade across systems and users |
Unlike traditional applications, where data exposure is typically tied to specific queries, AI systems generate new outputs based on learned representations. That makes leakage harder to predict and harder to contain.
What CISOs Should Do Now
Addressing AI data leakage requires shifting from reactive controls to lifecycle governance.
1. Discover Where Sensitive Data Enters AI Systems
Inventory which models exist, how they were trained, and which data sources they access. Many organizations underestimate the extent to which proprietary information flows into AI pipelines through fine-tuning, embeddings, or retrieval systems.
Without discovery, leakage risk is invisible.
2. Test for Data Exposure Before Production
AI systems should be evaluated for memorization and extraction risk before deployment. This includes adversarial prompt testing and simulated extraction attempts.
Using automated testing environments such as Cranium Arena, teams can assess whether models reproduce sensitive content or respond in ways that violate policy — before those behaviors surface externally.
3. Monitor Outputs in Real Time
Security doesn’t stop at launch.
Continuous monitoring is necessary to detect anomalous outputs, suspicious prompt patterns, and behavioral drift. With Detect AI, enterprises can gain visibility into model behavior in production, helping identify potential data leakage events that traditional logging tools overlook.
Monitoring must focus not just on inputs, but on outputs and patterns over time.
4. Establish Governance and Documentation Controls
Regulators increasingly expect transparency around how AI systems use data. Clear documentation of training sources, validation processes, and testing outcomes is essential.
Tools such as AI Cards help centralize model documentation, providing traceability across training, deployment, and monitoring stages.
Governance isn’t just compliance. It’s operational clarity.
Why This Is a Governance Issue, Not Just a Technical One
Data leakage from AI systems isn’t merely a vulnerability problem. It’s a governance failure if left unmanaged.
If your AI model reveals customer information, internal strategies, or proprietary algorithms, the reputational and regulatory consequences fall on your organization — not the model vendor.
The shift here is subtle but important: AI systems must be treated as high-value assets with behavioral risk, not just software components.
Lifecycle oversight — discovery, testing, monitoring, and governance — is what separates controlled AI from uncontrolled exposure.
Bottom Line
AI models don’t need to be hacked to leak data. They simply need access to it.
As AI becomes embedded in enterprise workflows, the risk of unintentional exposure grows. Training data, contextual interactions, and integrated systems can all contribute to leakage that traditional security tools were never designed to catch.
The organizations that scale AI safely won’t rely solely on perimeter controls. They’ll invest in visibility into how models are trained, how they behave, and how their outputs align with policy. AI doesn’t just change how software works. It changes how data flows.
The question isn’t whether AI can leak sensitive information. It’s whether you’ll see it before someone else does.
Explore how Cranium helps enterprises discover, test, monitor, and govern AI systems at scale: cranium.ai